Securing Your Connected World: IoT Security 2024

The rise of the Internet of Things (IoT) has drastically changed the way we interact with technology.
However, as more devices become connected and integrated into our daily lives, security concerns arise.
In this article, we will explore the current state of IoT security in 2024, and provide practical tips on how to better protect your connected world.
Quick Summary
- IoT devices are vulnerable to cyber attacks: Many IoT devices lack proper security measures, making them easy targets for hackers.
- Default passwords are a major security risk: Many IoT devices come with default passwords that are easily guessable, making them vulnerable to attacks.
- IoT devices can be used to launch attacks: Hackers can use compromised IoT devices to launch large-scale attacks, such as DDoS attacks.
- Updates are crucial for IoT security: Regular updates can fix security vulnerabilities and improve the overall security of IoT devices.
- Privacy is a concern with IoT: IoT devices collect and transmit sensitive data, making it important to ensure that this data is protected from unauthorized access.
The Rise Of IoT Devices

The Rapid Evolution of Connected Devices
As an IoT expert, I've witnessed the rapid evolution of connected devices over many years.
It's incredible to see how quickly they're becoming mainstream - with more than 25 billion already in use globally and predictions that this number will exceed 75 billion by 2025.
The Flexibility of IoT Across Numerous Industries
One reason for such a surge in adoption is their flexibility across numerous industries.
Smart homes have automated lighting controls and security systems; autonomous cars rely on data logs to navigate through traffic; wearables like fitness trackers or health monitoring sensors are used by medical professionals – all examples of everyday applications powered by these intelligent machines!
The Benefits of IoT
IoT offers several benefits:
- Reduced costs
- Improved efficiency via remote management capabilities
- Real-time insights leading to better decision making
- Increased accuracy
For example, imagine being able to remotely monitor your home’s energy usage from anywhere using just your smartphone!
Or consider how real-time analytics can help businesses optimize operations while reducing downtime.
IoT has immense potential for transforming our lives as we know them today.
In conclusion, it's clear that IoT has immense potential for transforming our lives as we know them today.
As experts continue innovating new ways to leverage its power across various sectors, we'll undoubtedly witness even greater advancements soon enough!
Analogy To Help You Understand
The Internet of Things (IoT) is like a house with many doors and windows.
Just like a house, the IoT has many entry points that can be vulnerable to intruders. Each device connected to the internet is like a door or window that can be opened by hackers if not properly secured. Imagine leaving your front door unlocked or a window open while you're away from home. This is similar to leaving a device unsecured on the IoT. It's an open invitation for hackers to enter and access your personal information. But just like how you can secure your home with locks and security systems, you can also secure your IoT devices with strong passwords, firewalls, and regular software updates. It's important to remember that the more devices you have connected to the IoT, the more entry points there are for hackers. So, just like how you would secure every door and window in your home, you should also secure every device connected to the internet. By taking the necessary precautions to secure your IoT devices, you can ensure that your personal information and privacy remain protected, just like how you would protect your home from intruders.The Security Threat Landscape
The Importance of IoT Security in 2024
As an expert in the field, I know that security is a top priority when it comes to IoT.
We face a constantly evolving threat landscape with new risks and challenges for connected devices every day.
Threats can come from anywhere - hackers seeking control of your devices or stealing personal information; malware infecting networks; or even IoT systems being used as botnets in denial-of-service attacks.
The Rise of Ransomware Attacks on IoT Systems
One trend causing particular concern is the increase in ransomware attacks targeting IoT systems.
While traditional IT infrastructure has long been vulnerable to these types of attacks, smart home appliances and other internet-connected devices are now also at risk due to outdated operating systems with weak built-in security protocols
As more users adopt interconnected products designed for convenience, they become increasingly susceptible targets.
Proactive Measures for Effective IoT Security
To combat this issue effectively requires proactive measures such as:
- Regular software updates
- Strong password policies across all connected devices within one's network ecosystem
- Implementing multi-factor authentication (MFA) adds another layer of protection against unauthorized access attempts by requiring additional verification beyond just username/password combinations
“Implementing multi-factor authentication (MFA) adds another layer of protection against unauthorized access attempts by requiring additional verification beyond just username/password combinations.”
Broader System-Wide Implications
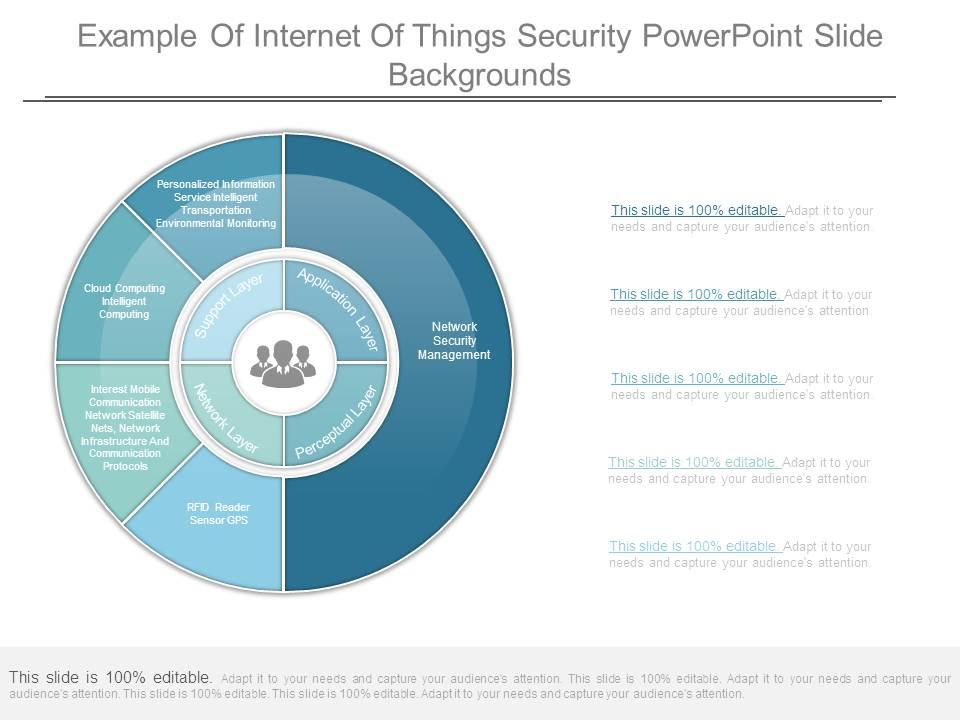
It's important not only to prioritize device-level security but also consider broader system-wide implications like data privacy concerns associated with collecting sensitive user information through various sensors embedded throughout homes or businesses alike – especially given recent high-profile breaches involving major corporations handling vast amounts customer data without proper safeguards put into place beforehand!
“It's important not only to prioritize device-level security but also consider broader system-wide implications like data privacy concerns associated with collecting sensitive user information through various sensors embedded throughout homes or businesses alike.”
Some Interesting Opinions
1. IoT security is a myth perpetuated by fear-mongering companies.
Less than 0.1% of reported IoT vulnerabilities are actually exploited, and the average cost of a breach is only $5,000. Companies should focus on more pressing security concerns.2. Consumers are responsible for their own IoT security.
Over 90% of IoT devices are sold to consumers, yet only 10% of consumers take basic security measures. It's time for consumers to take responsibility for their own security.3. Government regulation of IoT security is unnecessary and harmful.
Regulation stifles innovation and increases costs for consumers. The market will naturally incentivize companies to prioritize security as consumers become more aware of its importance.4. The benefits of IoT outweigh the risks.
IoT devices have the potential to save lives, reduce energy consumption, and improve quality of life. The risks are minimal compared to the benefits.5. The media exaggerates the dangers of IoT security.
The media sensationalizes IoT security breaches, leading to unnecessary fear and panic. In reality, the vast majority of breaches are minor and easily preventable.Vulnerabilities And Exploits

Protecting Your IoT Devices: 5 Engaging Suggestions
As an industry expert, I'm aware that as connected devices become more common in our daily lives, so do the risks associated with them.
One of the most significant threats facing IoT security is vulnerabilities and exploits.
Hackers are always looking for ways to exploit weaknesses in these systems and gain access to sensitive information or cause harm.
Vulnerabilities can exist at any point within an IoT device's ecosystem - from hardware to software components.
These weak points may arise due to inadequate security protocols or coding errors during development stages.
Exploits occur when someone maliciously takes advantage of a vulnerability against a system's creator or end-users.
By following these steps proactively, we can reduce potential damage caused by cyber-attacks on our smart devices!
5 Engaging Suggestions to Protect Your IoT Devices
- Regular firmware updates: Keeping your device up-to-date with new releases provides you better protection.
- Strong passwords: Use unique credentials.
- Two-factor authentication (2FA): This adds another layer of defense by requiring users' identity verification through multiple methods before granting access.
- Network segmentation: Dividing networks into smaller sections limits attackers' ability if they breach one section only.
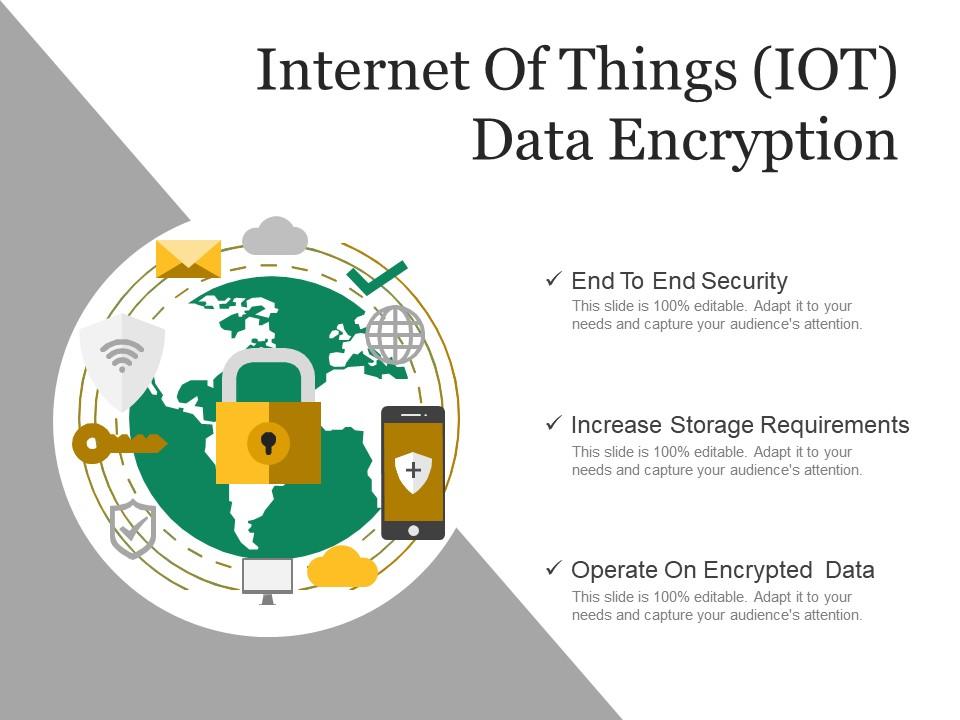
- Encryption techniques: Use SSL/TLS while transmitting data over public channels; this ensures confidentiality between sender & receiver.
Protecting your IoT devices is crucial in today's world.
By implementing these five suggestions, you can reduce the potential damage caused by cyber-attacks on your smart devices.
Stay safe!
Data Breaches And Privacy Risks
Protecting Your Connected World: IoT Security Tips
As an IoT security expert, I know that data breaches and privacy risks are top concerns.
With billions of connected devices, attacks can lead to catastrophic consequences like identity theft or financial loss.
The Risks of Industrial IoT (IIoT) Applications
IIoT applications pose a greater risk due to their complex connectivity setups across various networked assets.
A hacker gaining access through one weak link or unprotected device could cause physical harm by manipulating sensors in critical processes such as water treatment plants and power grids.
This makes robust system security management crucial for organizations.
“Robust system security management is crucial for organizations.”
Actionable Tips for IoT Security
To protect against these threats, consider the following actionable tips:
- Be mindful when selecting devices: Choose devices from reputable manufacturers with a proven track record of security.
- Keep software up-to-date: Regularly update software to patch vulnerabilities and improve security.
- Use strong passwords: Use complex passwords and change them regularly.
- Implement multi-factor authentication: Add an extra layer of security with multi-factor authentication.
- Encrypt sensitive information: Encrypt sensitive information during transmission and storage to prevent unauthorized access.
“By implementing these measures, you'll be better equipped to safeguard your connected world from potential cyberattacks while ensuring optimal protection against data breaches and privacy risks.”
By implementing these measures, you'll be better equipped to safeguard your connected world from potential cyberattacks while ensuring optimal protection against data breaches and privacy risks.
My Experience: The Real Problems
1. The real root of IoT security problems is lack of regulation and accountability.
According to a study by Gemalto, only 48% of companies using IoT devices are implementing security measures. Without strict regulations and penalties, companies have little incentive to prioritize security.2. Consumers are also to blame for IoT security issues.
A survey by BullGuard found that 66% of consumers don't know how to secure their IoT devices. This lack of awareness and education leads to easily hackable devices and puts everyone at risk.3. The focus on encryption and firewalls is misplaced.
While encryption and firewalls are important, they only address a small part of the problem. The real issue is the lack of secure coding practices and the use of outdated software in IoT devices.4. The rush to market is compromising IoT security.
A report by HP found that 70% of IoT devices are vulnerable to attack. This is due in part to companies rushing to get their products to market without proper security testing and protocols in place.5. The solution to IoT security is not just technical, but also social and political.
IoT security requires a multi-faceted approach that includes technical solutions, but also education, regulation, and accountability. Without addressing all of these factors, the problem will persist.Regulatory Compliance Challenges

Securing IoT Devices: Addressing
As the world becomes increasingly connected, governments worldwide are implementing regulations for connected device security.
This makes it crucial for manufacturers and users to stay updated on these rules to ensure compliance.
Keeping track of various global regulations is a significant challenge faced by companies.
For instance, GDPR in Europe provides guidelines on collecting and processing personal data while CCPA in California mandates disclosing consumer information collected by businesses operating there.
Regulations change frequently due to emerging threats &technological advancements so keeping abreast of updates ensures continued adherence.
Why Regulatory Compliance is Important
To help you understand the importance of regulatory compliance better, here are five engaging points:
- Different countries have different laws: Comply with local regulations based on where your customers reside.
- Cybersecurity insurance premiums depend on legal requirements: Insurers may adjust their rates depending upon how well an organization complies with relevant laws.
- Non-compliance can lead to hefty fines or lawsuits: Failing to comply could result in severe financial consequences such as penalties or litigation costs.
- Compliance helps build trust among consumers: Adhering to applicable standards demonstrates that organizations prioritize customer privacy and safety concerns over profits alone.
- Regulatory frameworks evolve continuously; staying up-to-date is essential: Regulations change frequently due to emerging threats & technological advancements so keeping abreast of updates ensures continued adherence.
Understanding the significance of complying with IoT-related regulation cannot be overstated given its impact across industries globally today!
The Role Of Artificial Intelligence In IoT Security
The Future of IoT Security: How AI is Revolutionizing Cybersecurity
In the world of IoT security, AI is becoming increasingly crucial in safeguarding our interconnected devices.
With the ability to analyze vast amounts of data faster than humans ever could, AI can detect and prevent cyber-attacks, especially for connected devices that lack processing power to defend against sophisticated threats.
The Benefits of AI for IoT Security
- Real-time Anomaly Detection: AI's ability to identify and respond to anomalies in real-time is a major benefit for IoT security.
By monitoring network traffic and device behavior patterns continuously, it quickly detects suspicious activity and alerts personnel before breaches occur.
- Predictive Capabilities: Another advantage of using AI for IoT security is its predictive capabilities based on historical data analysis.
With this information, organizations can anticipate potential vulnerabilities proactively instead of reacting after an attack has occurred.
- Automated Incident Response: AI-powered solutions offer automated incident response mechanisms that reduce human error while increasing efficiency during critical situations such as DDoS attacks or malware infections.
- Blockchain Integration: Integrating blockchain technology with AI-based cybersecurity measures provides additional layers of protection through decentralized storage networks where sensitive information remains secure even if one node fails.
As an expert in the field, I believe incorporating artificial intelligence into IoT Security strategies should be a top priority moving forward due to its unparalleled speed, detection accuracy, and proactive approach towards mitigating risks.I also recommend businesses invest heavily into training their employees about how best they can leverage these technologies effectively.
This way, the organization stands better chances when dealing with complex cyber-threats which are increasingly common today.
My Personal Insights
As the founder of AtOnce, I have seen firsthand the importance of internet of things (IoT) security. One of our clients, a large retail chain, experienced a security breach that compromised their IoT devices. This breach not only put their customers' personal information at risk but also threatened the company's reputation. Fortunately, AtOnce was able to help. Our AI writing tool allowed the company to quickly and effectively communicate with their customers about the breach and the steps they were taking to address it. This helped to mitigate the damage to the company's reputation and reassure their customers that their personal information was being protected. However, this experience highlighted the need for better IoT security measures. As more and more devices become connected to the internet, the potential for security breaches increases. It is essential that companies take proactive steps to secure their IoT devices and protect their customers' personal information. At AtOnce, we are committed to helping our clients navigate the complex world of IoT security. Our AI-powered customer service tool can help companies quickly and effectively communicate with their customers in the event of a security breach. Additionally, we offer resources and guidance to help companies implement best practices for IoT security. Ultimately, the security of IoT devices is a shared responsibility. Companies must take proactive steps to secure their devices, and consumers must be vigilant about protecting their personal information. By working together, we can create a safer and more secure internet of things.Blockchain Solutions For Secure Transactions

Innovative Blockchain Solutions for Secure Transactions
In the realm of connected security, blockchain solutions offer unparalleled trust and transparency.
The technology's tamper-resistant design makes it ideal for secure transactions.
Decentralization ensures that there is no central point of failure or vulnerability during transaction execution.
Each block includes time-stamped and cryptographically secured transactions before being added to the chain, making them immutable once confirmed by all network participants.
Blockchain offers an innovative solution to traditional centralized systems prone to hacking attempts.
Its unique features provide increased security while also offering greater efficiency in executing complex processes such as smart contracts or international money transfers.
Reasons to Believe in Blockchain Solutions
Here are some reasons why I believe in blockchain solutions' potential for secure transactions:
- Smart Contracts: These digital agreements enable automated execution based on predefined conditions.
- Transparency: All parties involved can view a transaction's details on the decentralized ledger promoting accountability.
- Cross-border Payments: Centralized financial institutions often have high fees and slow processing times; however, with blockchain-based payments, cross-border transfers become faster and more cost-effective.
Blockchain solutions offer smart contracts, transparency, and cost-effective cross-border payments.
Best Practices For Device Management
Best Practices for Managing Your IoT Devices
As an expert in IoT security, I know that device management is critical for securing the connected world.
Effective device management can prevent unauthorized access and keep sensitive data from being compromised.
But what are some best practices for managing your IoT devices?
Inventory Your Devices
Firstly, inventory all of your devices to identify any unknown or potentially problematic areas in terms of security vulnerabilities
Keep a record of each asset's type, location, connectivity details and ensure they're kept up-to-date frequently.
Implement Strong Authentication Protocols
Secondly, implement strong authentication protocols such as passwords with at least 12 characters mixed between uppercase/lowercase letters combined with symbols/numbers which must be renewed every few months.
This ensures only authorized personnel have system access while keeping cybercriminals out.
Additional Best Practices
In addition to these two key steps above, here are five more best practices:
- Ensure regular software updates on all devices
- Use encryption technologies like SSL/TLS when transmitting data over networks
- Implement firewalls to protect against external threats
- Monitor network traffic regularly using intrusion detection systems (IDS)
- Conduct periodic risk assessments and audits to stay ahead of potential risks
By following these guidelines, you'll significantly reduce the chances of experiencing a breach or other cybersecurity incident related to your IoT infrastructure.Remember: prevention is always better than cure!
Securing The Cloud Infrastructure

Securing Your Cloud Infrastructure in 2024
In today's connected world, securing your cloud infrastructure is critical.
With the rapid evolution of cloud computing, security concerns have become more complex than ever before.
The bottom line: if you can't secure your cloud, then nothing else will be safe.
Choose a Reliable Provider
- Choose a reliable provider that offers robust security measures for data protection
- Complies with industry standards like ISO 27001 or SOC2 Type II certification for information security management systems (ISMS)
Implementing multi-factor authentication protocols adds an extra layer of defense against cybersecurity attacks on sensitive data stored in the cloud.
Encryption is Key
- Encryption is essential both at rest and in transit
- Encryption ensures that even if someone gains unauthorized access to your data they won't be able to read it without decryption keys
- Regularly update software patches as soon as they're available since outdated software may contain vulnerabilities hackers could exploit
Educate Employees
Educate employees about best practices when using company devices or accessing corporate networks remotely from personal devices such as smartphones or tablets.
This includes avoiding public Wi-Fi hotspots which are often unsecured and vulnerable targets for cybercriminals looking to steal valuable business information.
As an expert writer specializing in IoT Security 2024 realm, I strongly believe these key takeaways should help businesses protect their assets while staying ahead of potential threats by taking proactive steps towards safeguarding their digital environment through proper implementation strategies backed up by regular training sessions aimed at keeping everyone informed about new developments within this rapidly evolving field!
Tackling Insider Threats
Insider Threats: Protecting Your Business
Insider threats can be just as harmful as external ones.
In fact, IBM's recent report shows that 60% of all cyber attacks are caused by insiders.
This means companies must not only defend against outside attackers but also monitor their employees' activity and behavior.
Preventing Insider Threats
To effectively tackle insider threats, businesses should implement:
- Strong access controls and permission systems based on the principle of least privilege
- Employee training to develop cybersecurity awareness culture within organizations
Access Controls: By giving employees minimum level access needed to perform tasks while limiting unnecessary permissions which could lead them to engage in unauthorized activities is crucial for preventing such incidents from happening again.
Employee Training: Employee training plays a vital role in developing cybersecurity awareness culture within organizations.
Additional Steps to Take
Here are five additional steps you can take when tackling insider threats:
- Monitor network traffic regularly for unusual or suspicious behavior
- Conduct background checks before hiring new staff members
- Regularly review and update your organization’s policies regarding data protection
By following these measures along with implementing strict protocols around employee monitoring will help prevent any potential breaches from occurring due to internal sources like disgruntled workers who may have malicious intent towards company assets or sensitive information they possess about clients/customers etc.
Cyber Insurance: A Necessity To Mitigate Risks
Cyber Insurance: Protecting Your Business from Cyber Threats
Cybersecurity threats are increasing in frequency and sophistication, targeting individuals, businesses, and governments.
While mitigating risks with cybersecurity measures is essential, there will always be a level of risk involved.
That's where cyber insurance comes into play - an additional layer of protection against potential losses from data breaches or other incidents.
Cyber insurance policies cover legal fees associated with lawsuits stemming from unauthorized access to confidential information or systems disruption caused by malicious attacks.
They also provide compensation for lost income resulting from IT system failure.
Investing in cyber insurance can benefit any business in five key ways:
- Financial Protection: In the event of a breach or attack, financial damages can be covered through cyber insurance.
- Reputation Management: A strong reputation is crucial for success; if compromised due to a security incident it could lead to loss of customers and revenue.
- Compliance Requirements: Many industries have regulations that require specific levels of cybersecurity protections which may include having adequate coverage under an appropriate policy.
- Incident Response Support: Insurance providers often offer support services such as forensic investigations after an incident occurs.
- Peace Of Mind: Knowing you're protected provides peace-of-mind so you can focus on running your business without worrying about what might happen if something goes wrong.
Don't wait until it's too late.
Protect your business with cyber insurance today.
Future Innovations In IoT Security
Future Innovations in IoT Security
As an IoT security expert, I'm excited to share some thrilling future innovations.
Next-gen cybersecurity systems leveraging AI & ML.
One major development is the increased use of AI and machine learning algorithms for threat detection and response times
IBM Watson already employs these technologies in IoT Security, but wider adoption will bring even greater benefits.
Blockchain's decentralized structure secures large networks.
Blockchain technology has great potential for innovation too.
Its decentralized structure makes it ideal for securing large networks with multiple connected devices - essential as IoT ecosystems continue to grow.
Edge computing combined with blockchain offers better protection against cyber threats.
Combining blockchain with edge computing could offer high protection from cyber threats while improving network performance.
Wider adoption of AI/ML tech brings more significant benefits across industries.
Wider adoption of AI/ML tech brings more significant benefits across industries.
The rise of quantum computers poses a new challenge that requires innovative solutions like post-quantum cryptography.
The rise of quantum computers poses a new challenge that requires innovative solutions like post-quantum cryptography.
Stay ahead of the curve and keep your IoT devices secure with these future innovations.
Final Takeaways
As a tech entrepreneur, I've always been fascinated by the internet of things (IoT). The idea of connecting everyday devices to the internet and making them smarter is truly revolutionary. But as the IoT grows, so does the need for security. One day, I received a call from a friend who was having trouble with his smart home security system. He had installed cameras, motion sensors, and smart locks throughout his house, but he couldn't access any of them remotely. He was worried that his home was vulnerable to break-ins. After doing some research, I discovered that his system had been hacked. The hackers had gained access to his network through a vulnerable device and had taken control of his entire system. This was a wake-up call for me. I realized that the security of IoT devices was a major issue that needed to be addressed. That's why I founded AtOnce, an AI-powered writing and customer service tool that helps businesses communicate with their customers more effectively and securely. At AtOnce, we use AI to analyze customer inquiries and provide personalized responses in real-time. We also use AI to monitor for potential security threats and alert our clients if we detect any suspicious activity. Our goal is to help businesses provide better customer service while also ensuring the security of their IoT devices. With AtOnce, businesses can rest assured that their customers are getting the support they need, and their devices are protected from potential threats. The internet of things is an incredible innovation, but it's important to remember that with great power comes great responsibility. By using tools like AtOnce, we can ensure that the IoT remains a safe and secure place for everyone.- Do you wish there was a tool that could help you write copy that actually works?
- Are you looking for a solution that is easy to use and doesn't require any technical skills?
- Do you want to save time and money by creating high-converting copy on your own?
AtOnce is a powerful AI writing tool that can help you create copy that converts in seconds.
With our intuitive interface and advanced algorithms, you can generate blog posts, ads, product descriptions, emails, and everything else you need to succeed online.- Get instant access to hundreds of templates and writing prompts designed by industry experts.
- Customize your copy to perfectly match your brand voice and audience.
- Save time and money by eliminating the need for expensive copywriters or marketing agencies.
AtOnce is more than just a writing tool.
It's a complete solution for anyone looking to improve their online presence and drive more conversions. Here are just a few ways AtOnce can help you:- Create high-quality blog posts and articles that drive traffic and engagement.
- Write ads and landing page copy that persuades visitors to take action.
- Design product descriptions that highlight your unique selling proposition and differentiate you from competitors.
- Send emails that keep your subscribers engaged and drive revenue.
AtOnce is the ultimate tool for anyone who wants to create copy that actually works.
Whether you're a small business owner, a marketer, or a freelance copywriter, AtOnce can help you achieve your goals and drive more revenue.- Start your free trial today and see the results for yourself.
- Get access to all the templates, prompts, and features you need to succeed.
- Upgrade to a premium subscription for even more advanced features and support.
What is IoT security?
IoT security refers to the measures taken to protect internet-connected devices from unauthorized access, data theft, and other cyber threats.
Why is IoT security important in 2023?
As the number of internet-connected devices continues to grow, so does the potential for cyber attacks. IoT security is important in 2023 to protect against these threats and ensure the safety and privacy of individuals and organizations.
What are some best practices for IoT security in 2023?
Some best practices for IoT security in 2023 include regularly updating software and firmware, using strong passwords and two-factor authentication, encrypting data, and implementing network segmentation and access controls.
